How to Secure the Data on Your Laptop
 Reader Jessica writes: I am an in-house investigator (not law enforcement) looking for laptop safety software. I've read on some of the "hardcore" techie pages that I need specialized encryption software to keep emails and files safe when I'm on my home wireless network. I'm planning on getting the Dell XPS 1710 for the road and working from home and know that it comes with the basic security suite. However, I'd like to be able to recommend something I can use on the laptop to the firm as well. I can't seem to convince the head honchos that information security is a huge problem!
Reader Jessica writes: I am an in-house investigator (not law enforcement) looking for laptop safety software. I've read on some of the "hardcore" techie pages that I need specialized encryption software to keep emails and files safe when I'm on my home wireless network. I'm planning on getting the Dell XPS 1710 for the road and working from home and know that it comes with the basic security suite. However, I'd like to be able to recommend something I can use on the laptop to the firm as well. I can't seem to convince the head honchos that information security is a huge problem!
Securing the data on a laptop computer requires a multitude of applications. The good news is that you're probably already running many of them. Here's a rundown on what you need, and what each application actually does.
Antivirus - The first line of defense; you are probably quite familiar with tools like Norton, PC-cillin, McAfee, etc. I've written about free antivirus options here.
Anti-spyware - The second line of defense; spyware blockers protect you from the other half of the malware out there. Install both Spybot and AdAware; both are free. I've written on how to clean a spyware infection here.
Firewall - A firewall protects you against direct attacks over the internet. Unlike viruses and spyware, these attacks don't arrive via a carrier application. Often they are "denial of service" attacks, which aim to simply disable your computer altogether, as long as the attack continues. The best firewall is the one on your router, so make sure it's turned out. Also turn on the built-in Windows Firewall. It does a fine job. I don't bother with additional firewalls unless the security need is extreme. In that case, ZoneAlarm is the one I'd recommend.
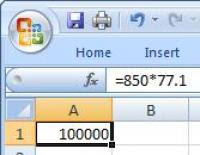
Data encryption - Things get more serious when we talk about encrypting the data on your PC. Encryption essentially scrambles everything on the computer unless the proper password is given to unlock it. You can also set up encryption to protect your email, but this is a more complicated process, as the recipient generally must also use the same encryption process to decode what you sent them. Just remember, encryption is only as good as the password you use to lock it. Windows Vista Ultimate Edition includes an encryption system called BitLocker. If you have Ultimate, definitely give it a spin. There are myriad encryption tools out there, most of which are free, which will encode your hard drive for you. Some are easy, some are difficult. Search around until you find one you like and which has positive reviews. You might start with FreeOTFE, which is pretty simple and rock solid. Be aware that encryption software will often slow down your PC considerably because of the complexity of the calculations it has to do.
Theft recovery - LoJack for Laptops (I've written about it many times) can help you out if your gear gets ripped off.
Additional tools (optional) - Many laptops include biometric scanners (fingerprint scanners) to help lock out unauthorized users. I find them more trouble than they're worth, but for sensitive data scenarios I'd recommend using one if your laptop includes it. Read the LoJack link above fore more commentary on how fingerprint scanners can interfere with LoJack.
Remember that all of these tools will only work as long as you keep them up to date with current data definitions, frequent scans, and with good passwords. Like most things, good security comes down mostly to common sense. Remember that
laptop theft is the most common computer crime out there. Keep your machine out of sight and secured with a cable lock whenever you're unsure of your environment's safety.